Ipsw Patch Tool 2 4 Windows 2012
Cydia running on an iPhone X.iOS jailbreaking is the of an Apple device for the purpose of removing software restrictions imposed by on, and operating systems. This is typically done by using a series of.
Jailbreaking permits in Apple's mobile operating system, allowing the installation of software that is unavailable through the official. Many types of jailbreaking are available, for different versions. Because Apple publicly disapproves of jailbreaking, Apple has implemented hardware and software fixes to the used in jailbreaks, meaning that many versions of iOS are not jailbroken immediately. It is analogous to on Android, although software unavailable on Google Play can be installed on Android without rooting. Contents.Motivations One of the reasons for jailbreaking is to expand the feature set limited by Apple and its App Store. Apple checks apps for compliance with its iOS Developer Program License Agreement before accepting them for distribution in the App Store. However, their reasons for banning apps are not limited to safety and security and may be regarded as arbitrary and capricious.
In one case, Apple mistakenly banned an app by a Pulitzer-Winning cartoonist because it violated its developer license agreement, which specifically bans apps that 'contain content that ridicules public figures.' To access banned apps, users rely on jailbreaking to circumvent Apple's censorship of content and features. Jailbreaking permits the downloading of programs not approved by Apple, such as user interface customization and tweaks.Device customization Since software programs available through and or (legacy) are not required to adhere to App Store guidelines, many of them are not typical self-contained apps but instead are extensions and customization options for iOS and its features and other apps (commonly called tweaks). Users install these programs for purposes including personalization and customization of the interface by tweaks developed by developers and designers, adding desired features and fixing annoyances, and making development work on the device easier by providing access to the filesystem and command-line tools.
Many Chinese iOS device owners also jailbreak their phones to install third-party character because they are easier to use than Apple's. Carrier unlocking Jailbreaking also opens the possibility for using software to unofficially unlock iPhones so they can be used with other carriers. Software-based unlocks have been available since September 2007, with each tool applying to a specific iPhone model and version (or multiple models and versions). This includes the, and models.
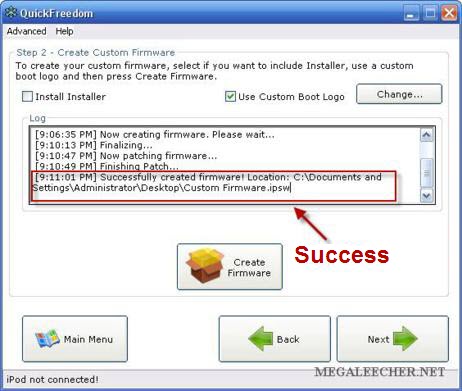
An example of unlocking an iPhone through a Jailbreak utility would be Redsn0w. Through this software, iPhone users will be able to create a custom and unlock their device. Moreover, during the unlocking process, there are options to install Cydia the iPad baseband.Installation of malware Computer criminals may jailbreak an iPhone to install malware or target jailbroken iPhones on which malware can be installed more easily. The Italian cybersecurity company, which sells hacking software to law enforcement agencies, advised police to jailbreak iPhones to allow tracking software to be installed on them. Software piracy On iPhones, the installation of consumer software is generally restricted to installation through the App Store. Jailbreaking, therefore, allows the installation of pirated applications.
It has been suggested that a major motivation for Apple to prevent jailbreaking is to protect the income of its App Store, including third-party developers and allow the buildup of a sustainable market for third-party software. However, the installation of pirated applications is also possible without jailbreaking, taking advantage of enterprise certificates to facilitate distribution of modified or pirated releases of popular applications. Types of jailbreaks.
A popular package manager installed on jailbroken devicesWhen a jailbroken device is booting, it loads Apple's own initially. The device is then and the kernel is every time it is turned on. Many different types of jailbreaks have come out over the years. An untethered jailbreak is a jailbreak that does not require any assistance when it reboots up. The kernel will be patched without the help of a computer or an application. These jailbreaks are uncommon and take a significant amount of reverse engineering to create.
A tethered jailbreak is the opposite of an untethered jailbreak, in the sense that a computer is required to boot, and the device will not boot by itself. While using a tethered jailbreak, the user will still be able to restart/kill the without needing to reboot. A mix between an untethered and a tethered jailbreak is also an option, namely semi-tethered. This type of jailbreak allows the user to reboot, but there will not be a patched kernel. Non-jailbroken functions will still run, such as making a phone call, texting, or using an app. To be able to have a patched kernel and run modified code again, the device must be booted using a computer. A type of jailbreak that has become popular in the recent years, is the semi-untethered variant.
This type of jailbreak is like a semi-tethered jailbreak in which when the device reboots, it no longer has a patched kernel, but the kernel can be patched without using a computer. The kernel is usually patched using a application installed on the device. Most recent jailbreaks have been the semi-untethered variant.Comparison to Android rooting Jailbreaking of iOS devices has sometimes been compared to ' of devices. Although both concepts involve privilege escalation, they differ in scope.
Some Android devices allow users to modify or replace the operating system after unlocking the. Moreover, nearly all Android phones have an option to allow the user to install unknown, 3rd-party apps, so no exploit is needed for normal.iOS is engineered with security measures including a 'locked bootloader' to prevent users from modifying the operating system, and to prevent apps from gaining root privileges; jailbreaking an iOS device to defeat all security measures presents a significant technical challenge. It violates Apple's end-user license agreement for iOS. Until 2015 sideloading apps in general was difficult for most individual users, requiring them to purchase developer membership, while corporations could install private applications onto corporate phones.
After 2015, this became free for all users, however doing so requires a basic understanding of Xcode and compiling iOS Apps. Apps installed this way have the restrictions of all other apps. In addition, alternative app stores utilising enterprise certificates have sprung up, offering modified or pirated releases of popular iOS applications and video games, some of which were either previously released through Cydia or are unavailable on the App Store due to them not complying with Apple developer guidelines.Security, privacy and stability The first, iKee, appeared in early November 2009, created by a 21-year-old student in the town of. He told Australian media that he created the worm to raise awareness of security issues: jailbreaking allows users to install an service, which those users can leave in the default insecure state. In the same month, reported on a new malicious worm compromising bank transactions from jailbroken phones in the, similarly affecting devices where the owner had installed SSH without changing the default password.In 2010 blogger, who is close to Apple, said that users misunderstood some jailbreak exploits and that they were more serious than they appear. He commented that 'it's odd how the press is mostly covering this as 'jailbreaking now more convenient' rather than 'remote code exploit now in the wild', pointing out that the exploit allowed the creator of a malicious website to take control of iPhones accessing it. Restoring a device with iTunes removes a jailbreak.
However, doing so generally updates the device to the latest, and possibly non-jailbreakable, version, due to Apple's use of. There are many applications that aim to prevent this, by restoring the devices to the same version they are currently running whilst removing the jailbreaks. Examples are, Succession, Semi-Restore and Cydia Eraser.In 2012, Forbes staff analyzed a UCSB study on 1,407 free programs available from Apple and a third party source.
Of the 1,407 free apps investigated, 825 were downloaded from Apple's App Store using the website App Tracker, and 526 from BigBoss (Cydia's default repository). 21% of official apps tested leaked device ID and 4% leaked location. Unofficial apps leaked 4% and 0.2% respectively.
0.2% of apps from Cydia leaked photos and browsing history, while the App Store leaked none. Unauthorized apps tended to respect privacy better than official ones. Also, a program available in Cydia called PrivaCy allows user to control the upload of usage statistics to remote servers.In August 2015 the malware was discovered that affects only jailbroken iPhones.
History of exploit-disabling patch releases Apple has released various updates to iOS that patch exploits used by jailbreak utilities; this includes a patch released in iOS 6.1.3 to software exploits used by the original iOS 6–6.1.2 jailbreak, in iOS 7.1 patching the Evasi0n 7 jailbreak for iOS 7–7.0.6-7.1 beta 3. Bootroom exploits (exploits found in the hardware of the device) cannot be patched by Apple system updates, but can be fixed in hardware revisions such as new chips or new hardware in its entirety, as occurred with the iPhone 3GS in 2009.On July 15, 2011, Apple released a new iOS version that closed the exploit used in 3.0.
The German had reported that JailbreakMe uncovered the 'critical weakness' that information could be stolen or unwillingly downloaded by iOS users clicking on maliciously crafted files. Before Apple released a fix for this security hole, jailbreak users had access to a fix published by the developer of JailbreakMe. On January 27, 2015, Apple released 8.1.3 that patched up the exploits used in jailbreak for 8.0–8.1.2.
It was not possible to jailbreak until the iOS 8.3 update. The iOS 9.1 update on October 21, 2015, included a patch for the Pangu iOS 9.0–9.0.2 Jailbreak.On August 13, 2015, Apple updated iOS to 8.4.1, patching the TaiG exploit. Apple Support. Retrieved March 12, 2019.
Chris Foresman (December 13, 2010). Retrieved August 2, 2011. Steve Kovach (13 April 2013). Business Insider. Ryan Singel (April 15, 2010). Retrieved February 12, 2011.
Archived from on 2014-07-15. Retrieved 2017-02-19. 2015-03-27. ^ Adam Dachis (March 14, 2011). Retrieved August 2, 2011.
Jenna Wortham (May 12, 2009). The New York Times. Retrieved August 2, 2011. Zdziarski, Jonathan (2008). Pp. 3–4. Landau, Ted (2009).
P. 107. Nathan T. Washburn (May 4, 2012).
HBR Blog Network. Harvard Business Review. Retrieved January 9, 2013. Brian X. Chen (August 7, 2009). Retrieved May 1, 2012. Ryan Block (September 11, 2007).
Retrieved February 1, 2014. Ian Paul (December 22, 2008). Retrieved May 1, 2012. Fleishman, Glen (2015-07-06). Retrieved 2 August 2015. Heath, Alex (2011-11-25). Retrieved 2 August 2015.

Hattersley, Lou. Retrieved 2 August 2015. Kazmucha, Allyson (2012-05-26). Retrieved 2 August 2015. Panzarino, Matthew (1 January 2013). The Next Web. Retrieved 4 May 2018.
^ Joseph Volpe (January 20, 2012). Retrieved January 20, 2012. Retrieved 26 October 2014. Archived from on May 21, 2011.
Retrieved October 26, 2014. Hildenbrand, Jerry (2 Feb 2012). Android Central.
Retrieved 9 July 2014. Apple Support.
Custom Ipsw Download
Retrieved 9 July 2014. Unauthorized modification of iOS is a violation of the iOS end-user software license agreement and because of this, Apple may deny service for an iPhone, iPad, or iPod touch that has installed any unauthorized software. Mayo, Benjamin (10 June 2015). Brigid Andersen (November 9, 2009). Retrieved October 26, 2011.
November 23, 2009. Retrieved April 10, 2010. Mikko (November 22, 2009). News from the Lab. Retrieved April 10, 2010. Gruber, John.
Daring Fireball. Retrieved 15 August 2015. Adrian Kingsley-Hughes (May 28, 2011). Retrieved November 14, 2012.
Sharon Vaknin (June 27, 2012). Retrieved November 14, 2012. Christopher Breen (December 29, 2008). Retrieved November 14, 2012. ^ Greenberg, Andy (February 14, 2012).
Retrieved February 15, 2012. Joseph Steinberg (August 31, 2015). Retrieved September 2, 2015. Retrieved 2015-06-20.
Robertson, Jordan (July 8, 2011). Archived from on July 11, 2011. Retrieved July 9, 2011. ^ Perez, Sarah. Retrieved 2015-11-11. Archived from on 23 September 2015.
Retrieved 10 October 2015. Apple Support. Retrieved 2017-03-19. Clover, Juli.
Retrieved 16 December 2019. ^ Duncan Geere (July 28, 2010). Retrieved October 26, 2012.
Greenberg, Andy. Retrieved 15 August 2015. Heath, Alex (2014-02-21). Retrieved 22 November 2015. Retrieved 15 August 2015.
Apple Support. Retrieved 2017-02-14. Rosalyn Page (August 5, 2010).
PC & Tech Authority. Retrieved January 21, 2013. (November 7, 2012). Retrieved November 13, 2012. Electronic Frontier Foundation. February 10, 2012.
Retrieved October 17, 2012. The Canadian Press (October 13, 2011). Retrieved October 17, 2012.
^ Pranesh Prakash (April 29, 2010). Retrieved November 10, 2012. ^ Nate Anderson (April 22, 2010). Retrieved November 10, 2012. Pranesh Prakash (May 23, 2012).
Retrieved November 10, 2012. (April 10, 2008).
Michael Geist. Retrieved October 26, 2012. Stephen Bell (September 30, 2011). ComputerWorld New Zealand. Archived from on September 30, 2011. Retrieved October 26, 2012. Kenny Chee (August 12, 2010).
Archived from on August 15, 2010. Retrieved November 10, 2012. Jim Martin (March 14, 2012). Retrieved January 21, 2013. Warwick Ashford (July 30, 2010). Computer Weekly. Electronics Weekly.
Retrieved January 21, 2013. Copyright Office, Library of Congress (October 2012). Federal Register. Retrieved February 3, 2014. David Goldman (July 26, 2010).
Retrieved September 11, 2010. Federal Register. The United States Government. October 28, 2015.
Retrieved November 20, 2015. ^. On The Media. July 30, 2010. Archived from on July 31, 2010.
Retrieved September 11, 2010. Leander Kahney (July 26, 2010).
Retrieved October 26, 2011. ^ Tim Wu (October 4, 2007). Retrieved October 26, 2011. (PDF). Retrieved September 11, 2010.
February 12, 2009. Retrieved July 17, 2009. Declan McCullagh (July 26, 2010). Retrieved October 26, 2011.
(PDF). Copyright Office. Retrieved October 31, 2012. ^ Timothy B. Lee (October 25, 2012). Retrieved October 26, 2012.
Android Police. Retrieved October 31, 2012. ^ Ricker, Thomas (July 10, 2007). Retrieved July 17, 2009. Topolsky, Joshua (August 6, 2007). Retrieved July 17, 2009.
Wilson, Ben (October 10, 2007). Archived from on July 19, 2009. Retrieved November 10, 2009.
Gregg Keizer (October 29, 2007). Retrieved August 25, 2011. Block, Ryan (February 12, 2008). Retrieved November 13, 2013. Charlie Sorrel (July 21, 2008). Retrieved November 2, 2011. ^ Philip Elmer-DeWitt (July 20, 2008).
Archived from on November 10, 2013. Retrieved October 26, 2011. Erica Sadun (July 20, 2008). Retrieved November 1, 2011.
Dev Team (May 2011). Dev Team Blog. Retrieved November 2, 2011. ^ iPhone Dev Team (December 27, 2011).
Dev Team Blog. Retrieved December 29, 2011. Charlie Sorrel (November 25, 2008).
Retrieved November 2, 2011. Daniel Pan (June 23, 2009). Retrieved November 2, 2015. ^ Elizabeth Fish (October 13, 2011). Retrieved October 26, 2011. Leslie Katz (July 3, 2009). Retrieved November 2, 2011.
Charlie Sorrel (November 5, 2009). Retrieved November 2, 2011. Thomas Ricker (June 7, 2011). Retrieved October 26, 2011. ^ Dan Goodin (May 3, 2010).
The Register. Retrieved October 26, 2011.
^ John D. Sutter (August 2, 2010). Archived from on February 3, 2012. Retrieved October 26, 2011. Sean Hollister (August 1, 2010).
Retrieved September 11, 2010. Andy Greenberg (August 1, 2011).
Retrieved December 23, 2012. ^ Eric Mack (July 6, 2011).
Retrieved October 26, 2011. P.
Connolly (July 15, 2011). Retrieved October 23, 2011.
Ipsw Patch Tool 2 4 Windows 2012 Download
jean (July 18, 2011). Sogeti ESEC Lab. Archived from on July 22, 2011. Retrieved October 23, 2011. David Murphy (October 9, 2010). Retrieved November 2, 2011. Charlie Sorrel (February 4, 2011).
Retrieved November 2, 2011. Elizabeth Fish (October 20, 2010). Retrieved November 2, 2011. Blair Hanley Frank (February 7, 2011). Retrieved November 2, 2011.

Edgar Alvarez (June 4, 2012). Retrieved June 16, 2012. ^ John Paul Titlow (January 20, 2012). Archived from on January 22, 2012.
Retrieved January 20, 2012. ^ Eric Mack (January 20, 2012). Retrieved January 22, 2012. ^ McKinley Noble (January 20, 2012). Retrieved January 22, 2012. Adrian Kingsley-Hughes (May 26, 2012).
Retrieved June 1, 2012. Retrieved June 3, 2013.
Retrieved June 3, 2013. Retrieved June 27, 2013. Retrieved 10 December 2014. Retrieved 3 July 2015.
@iH8sn0w (September 10, 2015). Retrieved October 10, 2015 – via.
Retrieved 16 October 2015. Retrieved 16 October 2015. Retrieved 16 October 2015. Retrieved 24 July 2016. Retrieved 21 March 2017.
Retrieved 2017-04-06. EverythingApplePro (2017-01-30), retrieved 2017-03-01. Retrieved March 22, 2019 – via Twitter. ^ Iqbal, Shaeel. Retrieved 2018-02-27.
Retrieved 2018-07-17. Retrieved March 22, 2019. Retrieved March 22, 2019. Retrieved March 22, 2019. ^. Twitter.com. ^.
March 22, 2019. Retrieved March 22, 2019 – via GitHub. Electra Team @electrateam (April 29, 2019). Retrieved 2019-06-19 – via. ^.
Retrieved 2019-07-19 – via Twitter. Retrieved 2019-09-28 – via Twitter. Security, Paul Wagenseil 2019-10-16T17:00:34Z.
Retrieved 2019-11-09. Apple, Download the iDB appAbout Contact Advertise Disclosure Privacy Cookie Unsubscribe2019 © iDownloadBlog com-This website is not affiliated with (2011-10-23). Retrieved 2019-11-09. iPhone Dev Team. Archived from on October 5, 2007. October 10, 2007. Archived from on April 2, 2012.
Retrieved August 23, 2012. Ryan Block (October 10, 2007). Retrieved August 24, 2012. PatrickJ (February 1, 2009).
Retrieved August 24, 2012. Justin Berka (February 3, 2009). Retrieved January 9, 2013. Ross Miller (June 20, 2009). Retrieved October 26, 2011.
Daniel Brusilovsky (July 3, 2009). The Washington Post. Retrieved October 26, 2011. Mike Keller (June 23, 2010). Retrieved October 26, 2011. John Herrman (June 8, 2010).
Retrieved November 2, 2011. Donald Melanson (October 20, 2010). Retrieved May 22, 2012.
^ Mathew J. Schwartz (July 7, 2011). Archived from on July 10, 2011. Retrieved October 23, 2011. ^ Mike Keller (August 23, 2011).
Retrieved October 23, 2011. ^ Sarah Jacobsson Purewal (October 18, 2011). Retrieved October 23, 2011.
^ iPhone Dev Team (March 7, 2012). Dev Team Blog.
Retrieved April 22, 2012. ^ Edgar Alvarez (April 21, 2012). Retrieved April 22, 2012. Dev-Team Blog. June 4, 2012. Retrieved May 30, 2013.
March 20, 2013. Retrieved May 30, 2013. ^. Archived from on February 4, 2013.
^. 2014-06-23. @tihmstar (August 6, 2017). Retrieved 2017-12-19 – via. Retrieved 2017-12-19.
Sparkes, Ben. Retrieved 2018-06-22.
Welcome to XPwn!The X is for 'cross', because unlike PwnageTool, this utility has nodependencies on proprietary, closed-source software and can potentially becompiled and used on any platform.This is a special proof-of-concept version available on any platform,compiled with static libraries to minimize potential issues (which is why theexecutables are a bit on the heavy side).The source is released under the terms of the GNU General Public Licenseversion 3. The full text of the license can be found in the file LICENSE. Thesource code itself is available at: What XPwn isA barebones pwnagetool implementation that is easily portable. What XPwn is NOTAn easy-to-use tool suitable for beginners. While it is possible easy to useuser interfaces will be developed for it eventually, it's mostly meant to bea toy for.nix geeks. Absolutely no support should be expected or will begiven.XPwn is also NOT winpwn. Winpwn will have things like easy package management,an actual, non-lame system of installing stuff.
I've seen the code for it, andit will be pretty awesome when finished. Those tasks are outside the scope ofXPwn. CreditsThis utility is merely an implementation of Pwnage, which is the work ofroxfan, Turbo, wizdaz, bgm, and pumpkin. Those guys are the real heroes.Also, the new super-awesome bootrom exploit is courtesy of wizdaz.MuscleNerd has put a lot of work into the 3G effort. The BootNeuter unlockfor first-generation iPhones packaged within is primarily his effort.Thanks also go to gray and c1de0x for their RCE efforts. Saurik is the authorof Cydia, included within.
Bugout was the lucky guy who did our first 3G tests.Thanks to chris for his hardware wisdom, Zf for his French humor, and pyteyfor the support on the serial stuff.idevice's 'ready for custom IPSW' art was graciously contributed by KinetiXXPwn attempts to use all the same data files and patches as PwnageTool toavoid duplication of present and future labor. I believe that wizdaz probablyput the most sweat into PwnageTool, and the pwnage ramdisk is the work ofTurbo.XPwn on Linux would not have been possible without libibooter, which waswritten by cmw, based on the Linux iPhone recovery driver written by geohot.Dripwn was created by Munnerz, specifically for installing iDroid.A special shout-out to cmw, who I have been helping with winpwn. He's put alot of hard work into winpwn, and should also be credited with doing some ofthe initial exploratory work with the undocumented DMG format. UsageThere are three utilities in this package, as well as the bundles andFirmwareBundles folders from PwnageTool, and Turbo's autopwn ramdisk. OverviewThe general series of steps should be to use ipsw to create a custom IPSW withthe user's preferences (done once per custom ipsw required), then itunespwn(done once per computer) so that future DFU restores will be made easier.Finally, either dfu-util (Mac or Linux) or idevice (Windows) should be used asnecessary on the iPhone to perform the actual exploit necessary to allow it toaccept our code.It is technically possible to skip itunespwn and just use idevice or skipidevice and just use itunespwn, but I recommend doing both. IpswNOTE: Important change for 2.0: (uncompressed) tarballs rather than paths arenow used for bundlesipsw is a more complex tool to generate custom IPSWs that you can restoreafter using xpwn (or any other pwnage-based utility).
This is important, sincethat's how the jailbreak actually occurs./ipsw -b -nowipe -bbupdate -s -r -memory -e ' -unlock -use39 -use46 -cleanup -3 -4.Yes, I know, confusing syntax. The first two options are the IPSW you want tomodify, and where you want to save the modified IPSW respectively.b and -rhave the same semantics and requirements as for xpwn. You can also specifyactions to exclude from the 'FilesystemPatches' section of the Info.plistfor your particular IPSW (in FirmwareBundles/).The most common use of the '-e' flag is to disable automatic activation, i.e.' -e 'Phone Activation'. Note that the double-quotes are necessary.-s allows you to specify the size of the system partition. This value isspecified in megabytes (NOT mebibytes)-memory allows you to specify that memory instead of temporary files should beused whenever possible (no longer the default).-nowipe disables Apple's wiping of the NAND (user data), before proceedingwith the restore.
This allows the restore to happen much, much more quickly.-bbupdate tells the restore ramdisk to attempt to upgrade your baseband. Thisis disabled by default for unlock safety reasons.-unlock, -use39, -use46, -cleanup, -3, and -4 are valid only if you merge theBootNeuter package. These provide instructions to BootNeuter (which providesunlocking for iPhones). If you choose to use BootNeuter, you must specify thelocation where the 3.9 and 4.9 bootloader can be found with the -3 and -4options. These cannot be included with xpwn due to copyright restrictions.-unlock specifies that you wish BootNeuter to unlock the phone (if it is notalready unlocked).use39 and -use46 instructs BootNeuter to either upgradeor downgrade your bootloader (if it is not already on the version you choose).-cleanup instructs BootNeuter to delete itself off of the iPhone after it iscomplete. If you do not specify -cleanup, BootNeuter will be accessible viaSpringBoard.The last options are for tar-files to merge.
All permissions and ownershipwill be preserved except for already directories that already exist. This isto prevent accidental clobbering (we're guessing you don't really want toalter permissions on existing directories). This behavior may change in thefuture.Told you it was a mess. ItunespwnThis Windows utility will replace a file in your%APPDATA%Apple ComputerDevice Support folder.
Ios 10 Ipsw
Subsequently, if you place your phone into DFU modeand iTunes recognizes it, Apple will automatically upload an exploit file ontoyour phone that will allow it to accept custom firmware (until it is turnedoff). This basically will allow you to restore any IPSW you want from thatversion of iTunes (provided you connect your phone in DFU mode).See the following section for detailed instructions on how to enter DFU mode.Usage: itunespwn The custom.ipsw is needed for the exploited WTF that was generated duringIPSW generation.
IdeviceThis utility replaces dfu-util for Windows, sidestepping the libusbrequirement and provides a more user-friendly way of guiding them throughDFU mode. Its arguments are analogous to dfu-util and more details can beread in that section. The difference is that iTunes' libraries are usedrather than the non-proprietary dfu-util.